We are aware of recent reports regarding targeted phishing attacks that have resulted in account takeovers of some Signal users, including government officials and journalists. We take this very seriously.
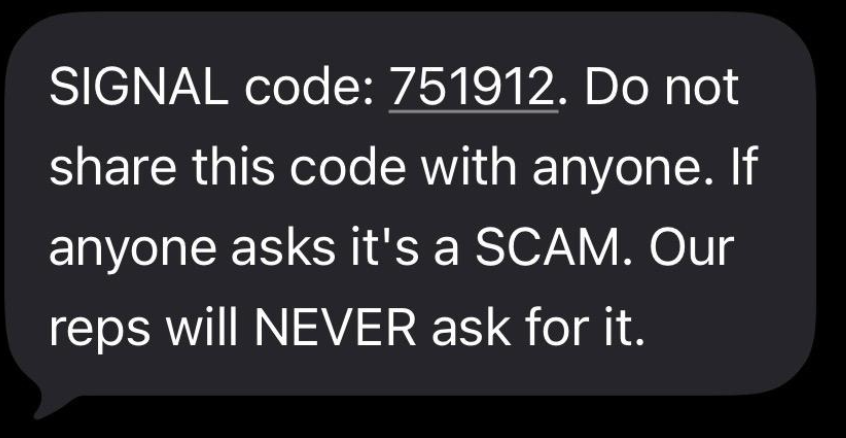
To be clear: Signal’s encryption and infrastructure have not been compromised and remain robust. These attacks were executed via sophisticated phishing campaigns, designed to trick users into sharing information – SMS codes and/or Signal PIN – to gain access to users’ accounts.